Overview:
The Cisco Application Policy Infrastructure Controller - Enterprise Module (APIC-EM) is Cisco's Software Defined Networking (SDN) Controller for Enterprise Networks (Access, Campus, WAN and Wireless).
Study Notes:
Performing an ACL-Based Path Trace
You can perform a path trace between two nodes in your network. The two nodes may be two hosts and/or Layer 3 interfaces.
| Note | The path trace application may display accuracy notes. Accuracy notes are red boxes that appears on a node or path segment indicating the accuracy of the computed path as a percentage. Place your cursor over the note to view suggestions of corrective actions to take to improve the path trace accuracy. For example, you may be prompted to enter port values and run the path trace again. |
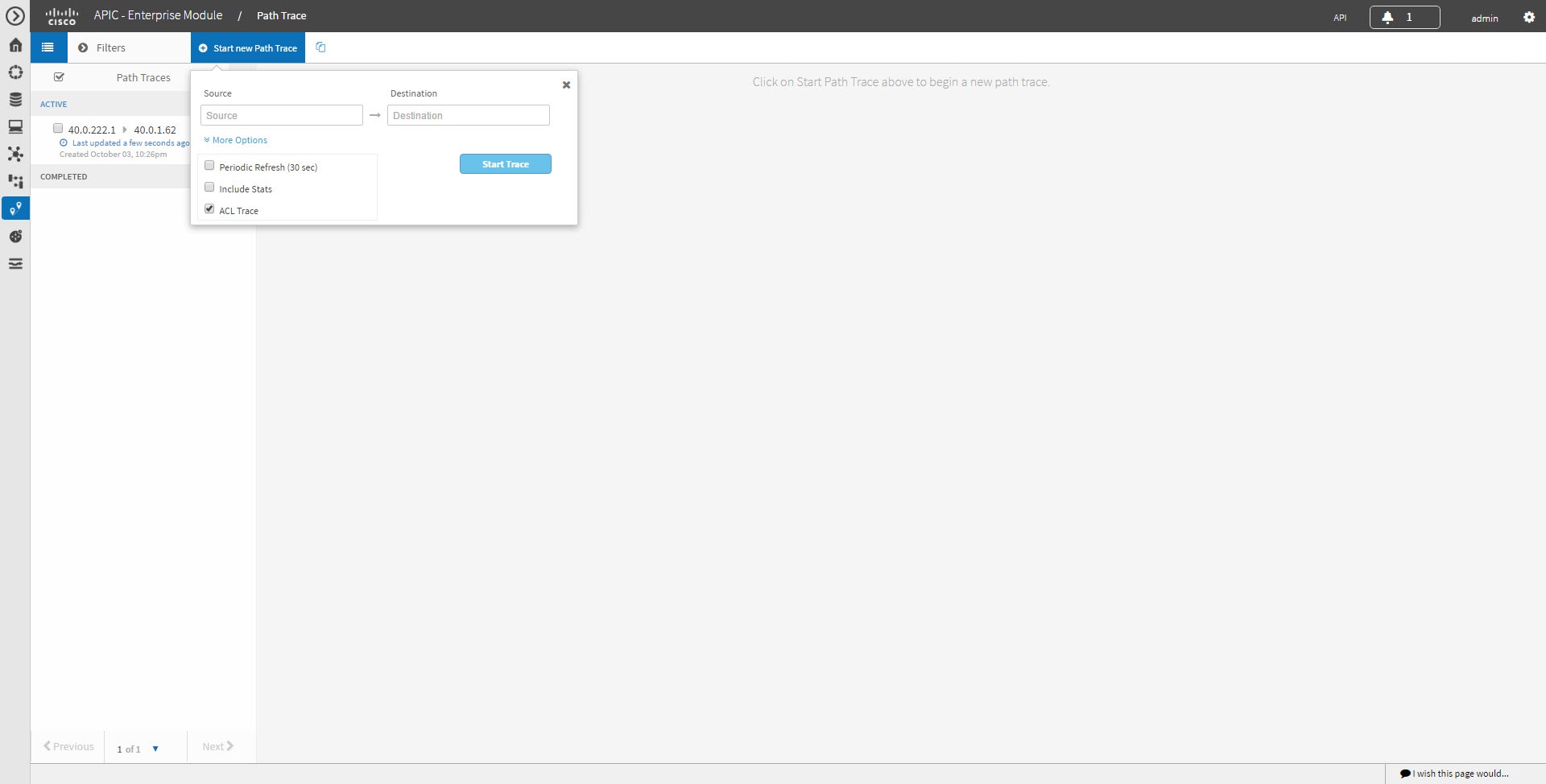
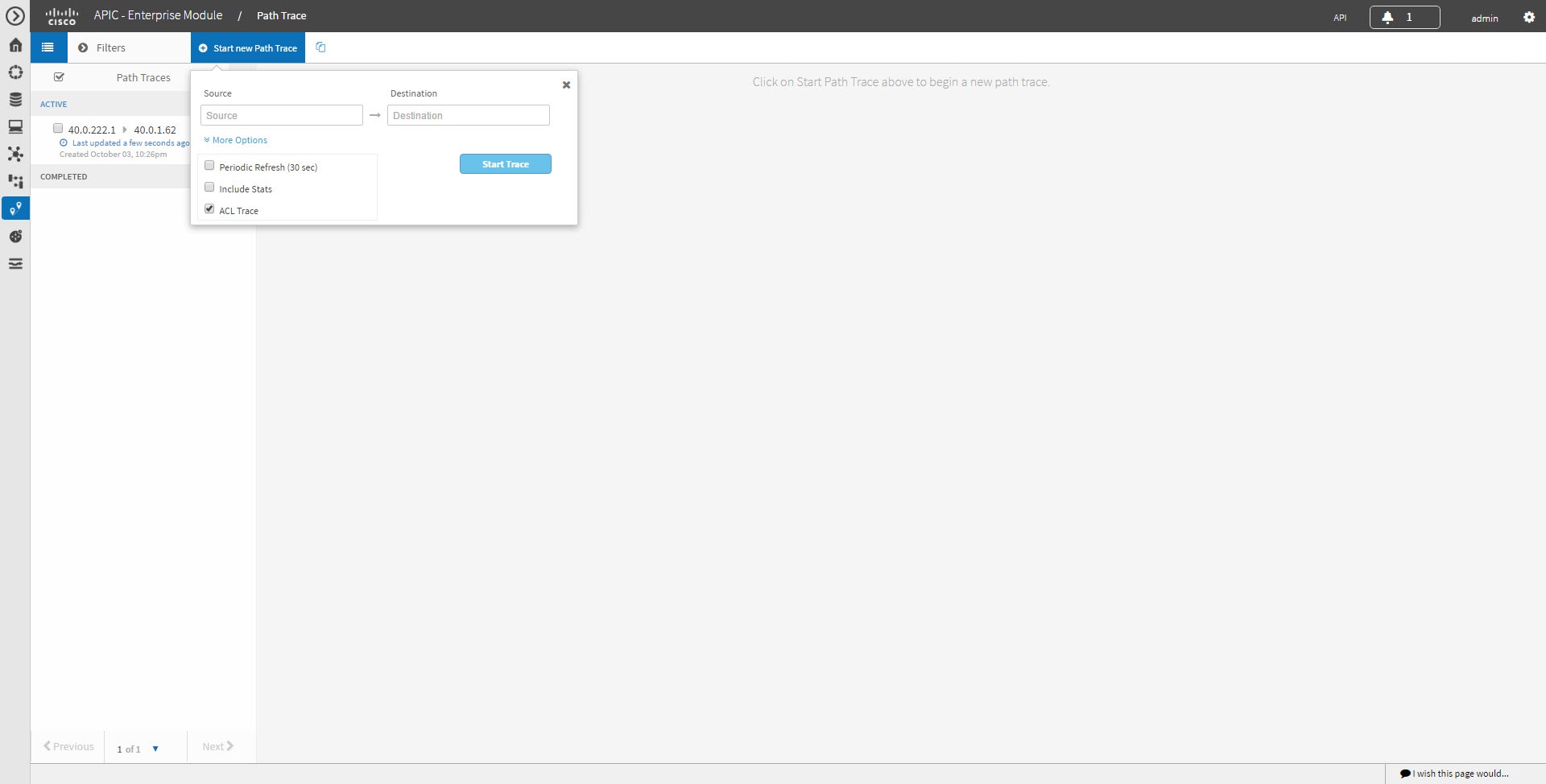
Figure 2. Path Trace Window Showing ACL Trace Selected
Before You Begin
Make sure that you have devices in your inventory. If not, discover devices using the Discovery function.
Ensure that the controller has SSH or Telnet access to the devices.
| Step 1 | In the Navigation pane, click Path Trace. |
| Step 2 | From the path trace toolbar, click Start new Path Trace. |
| Step 3 | In the Source field, enter the IP address of the host or the Layer 3 forwarding interface where you want the trace to start. If you enter the device IP address manually, you need to select the device from the list and then the interfaces for that device. |
| Step 4 | In the Destination field, enter the IP address of the host or Layer 3 forwarding interface where you want the trace to end. You can also enter an IP address of an unmanaged device (called an unknown destination). If you enter the device IP address manually, you need to select the device from the list and then the interfaces for that device. |
| Step 5 | (Optional)To configure source and destination ports or protocols, click More Options. |
| Step 6 | (Optional)In the Source Port field, enter the port number of the host where you want the trace to end. |
| Step 7 | (Optional)In the Destination Port field, enter the port number of the host where you want the trace to end. |
| Step 8 | (Optional)In the Protocol field, choose tcp or udp from the drop-down menu for the Layer 4 path trace protocol. |
| Step 9 | (Optional)To configure the path trace to refresh every 30 seconds, check the Periodic Refresh (30 sec) check box. |
| Step 10 | (Optional)To configure the path trace to collect additonal statistics, check the Stats check box and any of the following check boxes, as desired: QoS—Collects and displays information about quality of service. Interface—Collects and displays information about the interfaces on the devices along the path. Device—Collects and displays information, such as a device's CPU and memory usage. Perf Mon—Collects and displays performance monitoring information about the devices along the path. Note When you choose the Perf Mon option, APIC-EM enables performance monitoring configuration for all of the flows on the devices in the path. To proceed, you need to confirm this configuration. |
| Step 11 | Select the ACL Trace check box to run an ACL-based path trace. |
| Step 12 | Click Start Trace. Review the path trace output. For more information, see Understanding ACL Path Trace Results. |
| Step 13 | Unless you performed a path trace to an unknown destination, you can view the path trace in the Topology window. To do so, click View in Topology. The Topology window opens with the path trace highlighted in your network. For more information about the Topology window, see the Cisco Application Policy Infrastructure Controller Enterprise Module Administrator Guide. Note If you added location markers for your devices, the location markers appear in the Topology map. Click a location marker to display the Topology for that location. |
Understanding ACL Path Trace Results
An ACL path trace shows whether the traffic matching your criteria would be permitted or denied based on the ACLs configured on the path.
The following rules effect the ACL path trace results:
- Only matching ACEs are reported.
- If you leave out the protocol, source port, or destination port when defining a path trace, the results include ACE matches for all possible values for these fields.
- If no matching ACEs exists in the ACL, the flow is reported to be implicitly denied.
Figure 5. Path Trace Window Showing ACL Trace Selected
| Icon | Description |
|---|---|
| There are ACLs that permit the traffic applied on the interface. | |
| Traffic may or may not be blocked. For example, if your traffic matches a deny access control entry (ACE), traffic is denied. However, if your traffic matches any other ACEs, it is permitted. You can get this type of results if you leave out the protocol, source port, or destination port when defining a path trace. | |
| There is an ACL on the device or interface that is blocking the traffic on the path. | |
| There are no ACLs applied on the interface. |
Links: